Share via:
- Updated on: April 9, 2026
- France dominates global crypto kidnappings – 80% of European incidents, at least 40 since 2017 – in a category growing 75% annually. Structured criminal networks exploit surveillance, insider data, and family coercion to customize ransom demands.
- A French tax agent, arrested in June 2025, sold crypto investor profiles to organized crime via government software, while breaches at Global-e (a cross-border e-commerce order fulfillment service provider for Ledger) and Waltio created three distinct criminal data pipelines.
- The EU’s DAC8 requires identity and portfolio reporting, mirroring the framework that was exploited, while MiCA concentrates the risk further: regulations intended to protect investors financially are exposing them physically.
- France’s crypto violence now targets executives, families, magistrates, and anonymous investors across three models: kidnappings, forced home transfers, and corporate targeting. The separation of the recruiter and executor roles has resulted in zero final convictions, thereby sustaining criminal impunity.
- Every coerced transfer, including €900,000 in Bitcoin sent at knifepoint, is permanently recorded on-chain, giving investigators an indelible evidence trail. Crystal’s analytics equips PNACO and TRACFIN to follow it, while real-time VASP monitoring can intercept coerced transfers before funds move.
To find out what compliance teams, law enforcement officials, investigators and investors should do to counter the ongoing threat, read on.
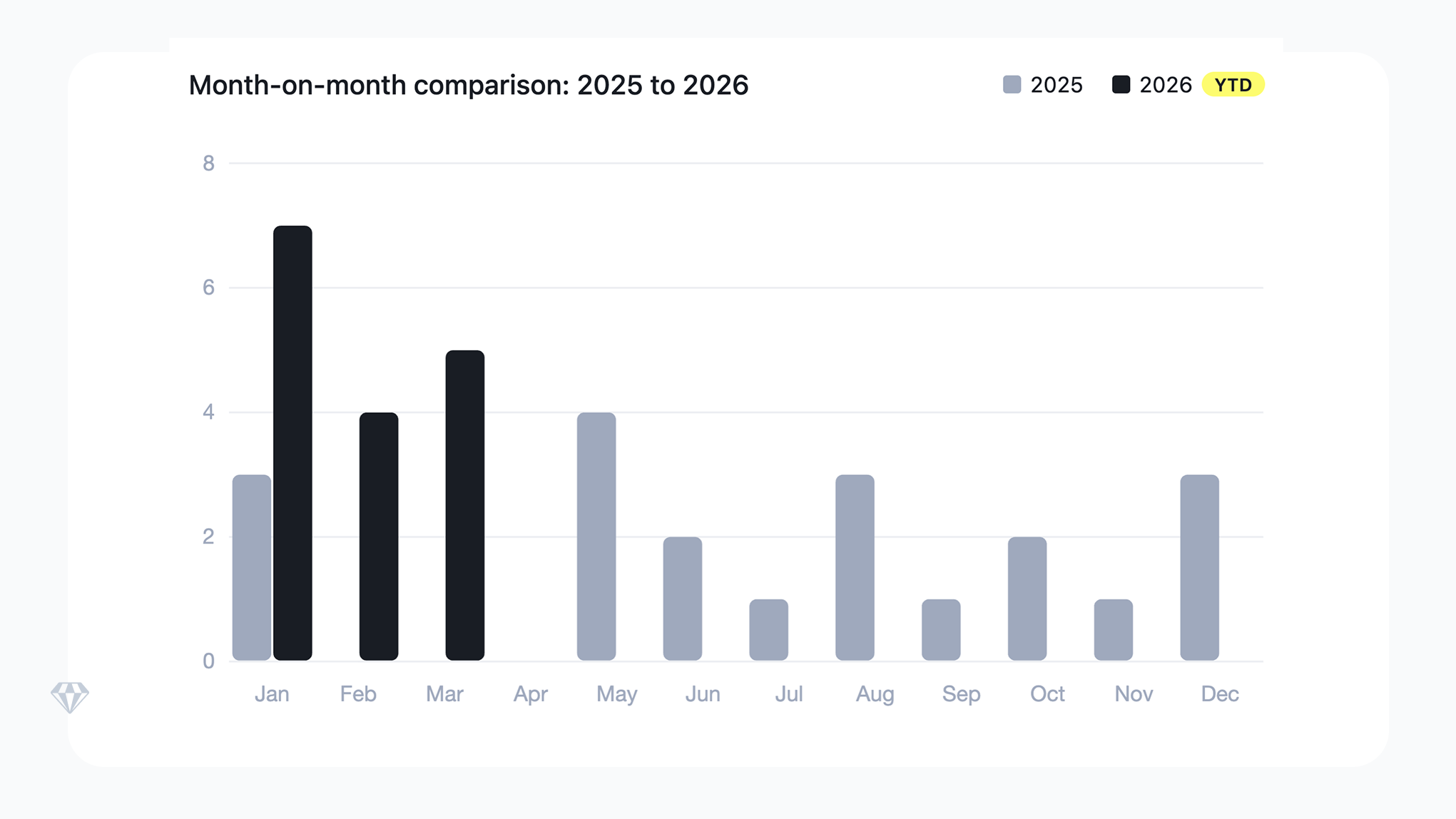
France recorded 16 crypto-related kidnappings and violent assaults in Q1 2026 alone, on top of 20-plus in 2025.:
- In January 2026, masked men abducted a retired couple in Sallanches, demanding €8M from their son, a digital assets professional whose identity and holdings the attackers already knew.
- Weeks later, in Le Chesnay, a couple opened their door to men posing as police; one held a knife to her while her partner transferred €900,000 in Bitcoin under duress, remotely directed via video call.
- Between these incidents, a magistrate and her mother were held for 30 hours, Binance France’s CEO survived a home invasion, and a crypto influencer’s father was abducted and doused in gasoline.
Disturbingly, the intelligence enabling every attack was traceable directly back to France’s own regulatory infrastructure, both public and private.
Data Source: Fibo-crypto, Github (courtesy of Jameson Lopp).
The scale of the problem: France now leads the world in this crime category
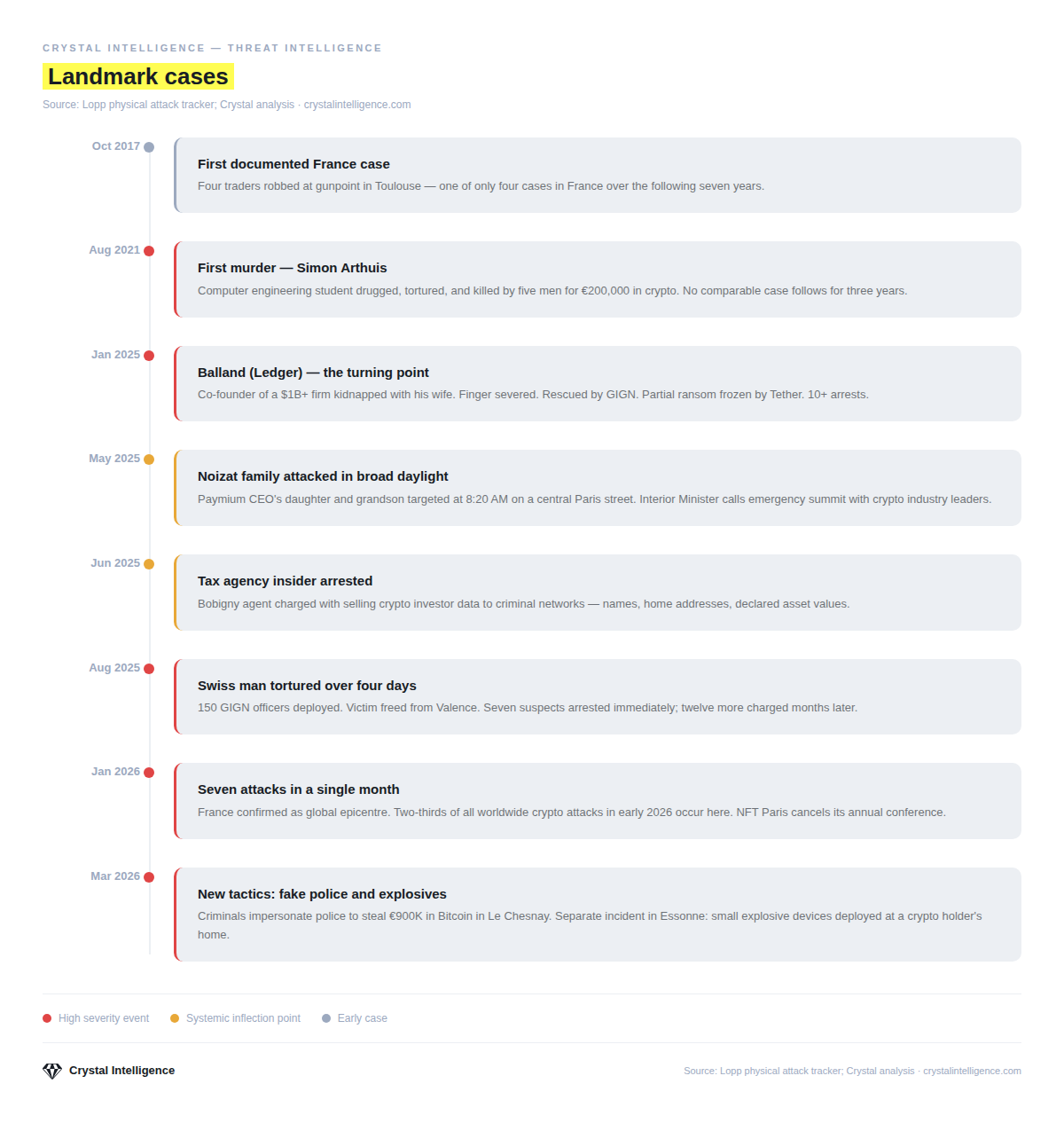
Since 2017, approximately 40 kidnappings and violent coercion attempts targeting crypto holders have been documented in France. There were 20 or more in 2025 alone, and by May of that year, an all-arms meeting between French authorities and crypto industry role-players was deemed necessary.

Above: Chart illustrating the progression of France’s reported crypto kidnappings and assaults since the first in 2017 up to Q1, 2026. Of 40 recorded incidents, 20 occurred in 2025 alone, and a further 16 by the end of March 2026 sounds a grim warning about what the future could hold without action. Data Source: Fibo-crypto, Github (courtesy of Jameson Lopp)
2026 brought no respite. The first quarter produced another 16 attacks, demonstrating the escalation of the phenomenon. France’s National Anti-Organized Crime Prosecutor’s Office (PNACO), established under the Narcotraffic Law in June 2025 and active since January 5, 2026, was handling at least six crypto-linked files by January 9, 2026.
Data Source: Fibo-crypto, Github (courtesy of Jameson Lopp).
France accounts for 80% of European cases and, with 20 of 74 globally tracked attacks in 2025, leads the world in this category. Blockchain security company CertiK’s February 2026 report counted 72 verified physical coercion incidents in 2025 – a 75% year-on-year increase – with physical assaults up 250%.
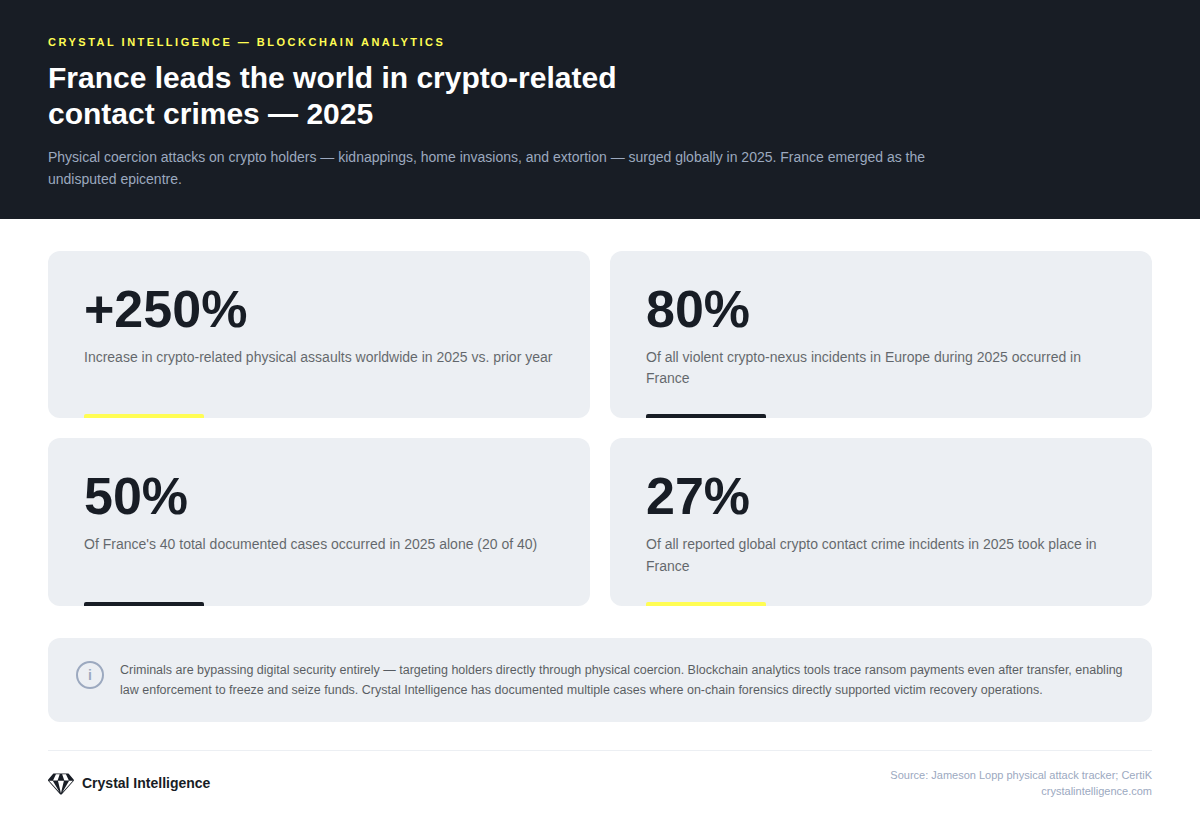
Source: Fibo-crypto, Github (courtesy of Jameson Lopp), and Certik.
These are not opportunistic attacks; instead, networks deploy surveillance, use family connections and set calibrated ransom demands. This intelligence implicates both the French state and the private sector.
The €800 target list: how criminal networks build their intelligence through three pipelines
The first pipeline was identified on June 30, 2025, when a tax official was taken into custody after investigators traced unauthorized searches in Mira, the French tax administration’s internal software, to a network selling target profiles for roughly €800 each. Investigations revealed the official’s workstation ran searches on crypto specialists, investors, and high-profile individuals.
The attorney general concluded the agent had taken advantage of the official role to serve a seasoned criminal. Authorities are now investigating whether other tax officials were compromised by the same network, making this agent potentially one node in a broader intelligence operation.
A second pipeline emerged on January 5, 2026, when Global-e, the cross-border e-commerce order fulfillment service provider for Ledger, a major crypto hardware wallet manufacturer and issuer in France, disclosed a breach exposing names, contact information, shipping addresses, and order records. A confirmed hardware wallet purchase tied to a home address is enough to physically locate a crypto holder.
A third pipeline appeared weeks later: Waltio, a French crypto tax service, was hacked, exposing investment amounts, transaction histories, and verified identification – the most financially precise target list yet.
Together, these three pipelines expose a threat the compliance industry has not adequately addressed: the data that agencies and platforms are required to collect for legitimate regulatory purposes is becoming a primary intelligence resource for organized crime.
The regulatory paradox: DAC8, MiCA and the data concentration problem
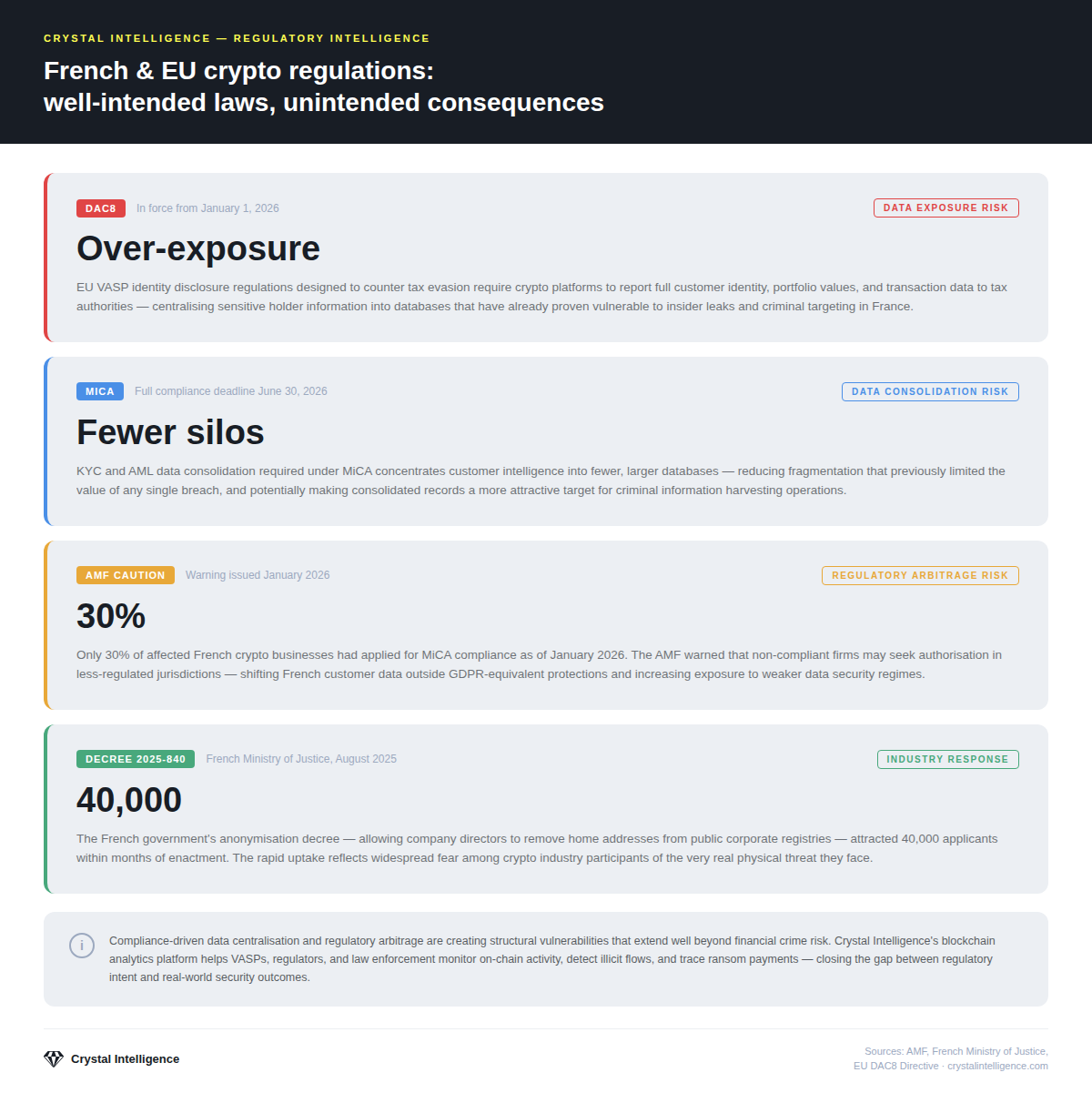
Since January 2026, the EU’s Directive on Administrative Cooperation (tax transparency for crypto-assets), or DAC8, has required virtual asset service providers to report user identities, tax IDs, portfolio values, and transaction totals to tax authorities, closing evasion loopholes but creating security risks.
DAC8 creates the first structured government database linking verified identities to confirmed crypto holdings, which is precisely the intelligence the compromised tax official’s network exploited. A broader collection across more agencies and access points multiplies the insider compromise, as her case demonstrated.
Meanwhile, France’s Markets in Crypto-Assets Regulation (MiCA) compliance deadline is June 30, 2026. In January 2026, the French Financial Markets Authority AMF flagged 90 unlicensed crypto companies: 40% didn’t intend to apply, 30% hadn’t responded at the time, and only 30% had applications in progress. Non-compliant firms must cease operations in July 2026. The AMF reiterated this reminder in February 2026.
MiCA’s data consolidation requirements concentrate know-your-customer (KYC) and DAC8 data in fewer, larger platforms, raising the criminal breach payoff for each. Additionally, the AMF has flagged that firms may be seeking licenses in weaker jurisdictions to use EU passporting rights, thereby routing French customer data through less secure environments.
Ironically, the result is that the regulatory architecture designed to protect investors financially is, unwittingly, the infrastructure that can endanger them physically. France’s August 22, 2025, decree allowing address anonymization, which drew 40,000 requests within months, demonstrates that the state recognizes this. However, recognition isn’t resolution: DAC8 security standards and platform monitoring must reflect what that data enables.
A widening target pool and a shifting threat environment
The clearest trend in the January – March 2026 series is that attackers are no longer limiting themselves to crypto industry insiders. The French Interior Ministry explicitly acknowledged a shift in the selection of criminal operations targets in January 2026, stating that the threat now also reaches private individuals.
The January attacks hit crypto executives and their immediate families. The February kidnapping of a sitting magistrate who had no personal crypto involvement and was targeted only because of her partner’s job showed that proximity to the industry is now enough. The Le Chesnay attack in March went further: a suburban couple that had no publicly known crypto profile was exposed only through data that placed them in the target pool.
Three operational models have run through this violent series:
- Direct corporate targeting involves targeting known industry role-players, rather than working through family proxies. Examples of this operational model include the attempted home invasion of Binance France CEO David Prinçay in February 2026 and the assault on a crypto influencer’s father in March 2026.
- In proxy kidnappings, the family member/s of named industry figures with no direct crypto involvement are seized to pressure the actual holder, such as the Sallanches retired couple, the Isère magistrate, and the 74-year-old tortured in Voiron over 16 hours. Ransom demands in this category ran from €1 million to €8 million.
- In home invasion and forced-transfer operations, such as Le Chesnay, Verneuil-sur-Seine, and Manosque, attackers entered the properties and compelled on-the-spot transfers, with amounts reflecting the quality of their pre-attack intelligence on holdings.
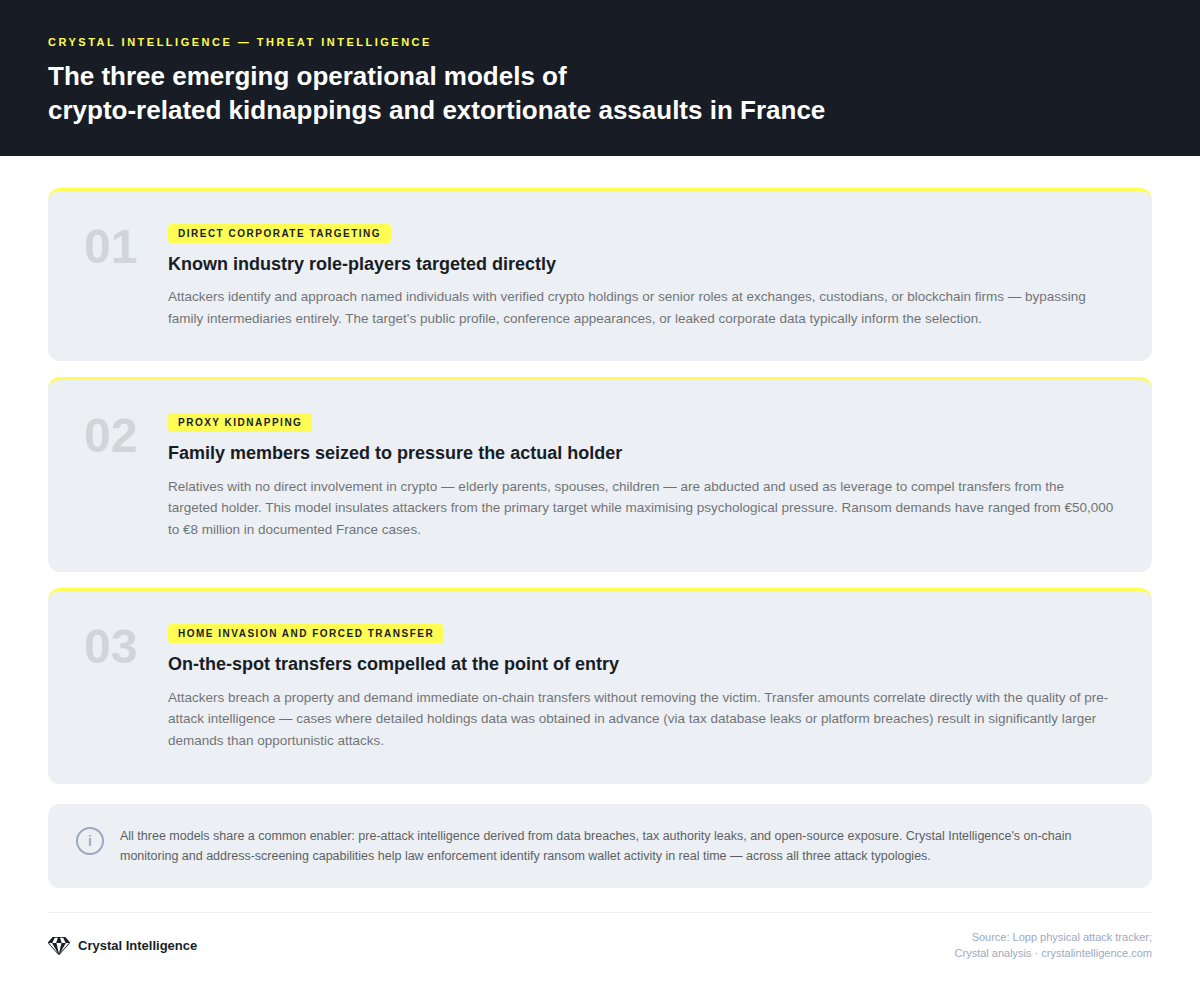
All three attack models share one structural feature: recruiters and executors are kept separate. Those arrested are predominantly young, low-level operatives recruited via Telegram and paid little or nothing. No final convictions have been secured in a French crypto extortion case, and the planning infrastructure remains unprosecuted. The Le Chesnay remote director, running the attack by video call, represents the clearest evidence of a command structure that conventional arrest strategies can’t yet reach.
Following the money: blockchain analytics as an investigative tool
Every crypto ransom payment criminals collect is a tactical error: each transfer is permanently recorded on a public blockchain. In the cases of the €900,000 forced in Le Chesnay and the €15,000 extracted in Verneuil-sur-Seine, every transaction is traceable evidence against the perpetrators.
PNACO’s investigations include money laundering charges because post-transfer blockchain activity is often the strongest evidence available. Once ransom payments land, funds must move- i.e., consolidated, mixed, and converted – and each step generates on-chain data. Crystal’s wallet clustering and transaction graph analysis can trace flows through mixers to exchange deposits, where subpoenas can identify who converted the proceeds.
The Le Chesnay transfer – €900,000 in Bitcoin, a single transaction on a documented date, known to have been made under duress – is an unusually clean on-chain starting point for investigators. For VASPs, the pattern was likely detectable before completion: atypical timing, dormant wallet activity, rapid, large outflows and high-risk destinations. Platforms with real-time transaction monitoring can pause transfers, conduct enhanced due diligence, and file suspicious activity reports. The victim’s platform had the technical capability to intervene.
Crystal’s analytics equip PNACO and TRACFIN to trace transactions, identify entities and build prosecution-ready evidence. For VASP compliance teams, real-time monitoring detects patterns of coerced transactions. This is what MiCA requires, and what any platform with a genuine duty of care is ethically obliged to deliver.
What compliance teams, investigators and platforms should do now
France’s crisis is a portent of what could come: DAC8 centralization, MiCA consolidation, rising valuations, and organized crime’s appetite for physical extortion have combined into something that won’t stay within French borders. Europe already accounts for 40% of global crypto-related physical attacks, and the enabling infrastructure is in place across the EU.
For VASP compliance teams: Audit KYC and DAC8 access controls, update transaction monitoring to flag coerced-transfer patterns, and recalibrate suspicious activity reporting to treat physical extortion as a threat category. While MiCA sets the scene, the institutions playing their part are exposed.
For law enforcement and investigators: On-chain evidence moves fast, and investigators without blockchain analytics capability consistently arrive too late. The PNACO model works only if investigators can follow transactions before they clear through mixers or cross jurisdictions. Le Chesnay – a large transfer with a clean timestamp and no interdiction – illustrates the cost of that gap.
For policymakers and platform operators: France’s August 2025 address anonymization decree deserves EU-level attention. Any institution holding DAC8 data should demonstrate security standards proportionate to the nature of that database: it is a consolidated record of high-value crypto holders, addresses, and holdings. Criminal networks have already exploited such data, and 16 attacks in Q1 2026 alone show that online risks have real-world consequences.
All these role-players will closely follow the legislative progress of the National Assembly’s Bill No. 2115, Amendment CF64, adopted on December 9, 2025. To improve the tax authorities’ oversight of user-hosted crypto-asset wallets- i.e., not administered through regulated intermediaries and therefore invisible to officials -CF64 obliges crypto owners with portfolios worth€5,000or more to report their holdings. Intended to improve tax collection and combat tax evasion, the Bill, if passed, could draw unintended attention from and targeting by sharp-eyed criminals of a new category of victim: ordinary middle-income people with no high-end industry connections or opulent crypto wealth, simply trying to save for their futures.
Compliance without security is not compliance
The 2026 attacks in France show what happens when incoming regulations outpace the security systems meant to support them. While the data requirements are legitimate, the institutions holding that data may be found wanting. Which means compliance – the thing regulators built to protect investors – is being turned against them instead.
The criminals targeting France’s crypto holders made one mistake: they used a traceable asset class to collect ransoms. That mistake is recoverable – but only if the platforms, investigators, and regulators involved have the tools to recover it, and the willingness to treat data security as part of their compliance obligations – not an afterthought to them.
Crystal Intelligence works with exchanges, financial institutions, law enforcement, and regulators across Europe to address exactly this. Transaction monitoring can flag coercion patterns early. Blockchain tracing gives investigators the evidence trail they need to build a case. And compliance tooling can satisfy MiCA and DAC8 requirements without leaving sensitive data exposed in ways that make the next attack easier.
Crystal Intelligence provides blockchain analytics and compliance infrastructure for financial institutions, exchanges, and law enforcement agencies globally. To learn how Crystal can enhance your compliance program or investigative capabilities, request a platform demo.